- Pro
- Security
Don't leave your OpenClaw with an easy password
When you purchase through links on our site, we may earn an affiliate commission. Here’s how it works.
 (Image credit: Fortune)
(Image credit: Fortune)
- Copy link
- X
- Threads
Sign up for breaking news, reviews, opinion, top tech deals, and more.
Contact me with news and offers from other Future brands Receive email from us on behalf of our trusted partners or sponsors By submitting your information you agree to the Terms & Conditions and Privacy Policy and are aged 16 or over.You are now subscribed
Your newsletter sign-up was successful
An account already exists for this email address, please log in. Subscribe to our newsletter- Oasis security researchers find a high-severity flaw in OpenClaw AI agent
- Exploit allowed malicious websites to brute-force local gateway authentication and gain full control
- Vulnerability patched within 24 hours; users urged to upgrade to version 2026.2.25 or later
OpenClaw, the vastly popular open source AI agent platform, was vulnerable to a high-severity flaw which allowed threat actors to steal sensitive data from target computers with relative ease, experts have warned.
The bug was discovered by security researchers Oasis, and was patched following responsible disclosure.
For those unfamiliar with OpenClaw, it is an AI agent that users install on their computers and interact with through a web dashboard or terminal. The tool connects to calendars, messaging apps, and can respond to emails, set up calendar events, and more. It is currently one of the most popular AI projects, with more than 100,000 stars on GitHub.
You may like-
 Moltbot is now OpenClaw - but watch out, malicious 'skills' are still trying to trick victims into spreading malware
Moltbot is now OpenClaw - but watch out, malicious 'skills' are still trying to trick victims into spreading malware
-
 Microsoft says OpenClaw is "not appropriate to run on a standard personal or enterprise workstation" — so should you be worried?
Microsoft says OpenClaw is "not appropriate to run on a standard personal or enterprise workstation" — so should you be worried?
-
 OpenClaw AI agents targeted by infostealer malware for the first time
OpenClaw AI agents targeted by infostealer malware for the first time
Brute forcing the password
But the very design of the tool left a gaping security hole which, according to Oasis, is relatively easy to exploit. It doesn’t require a third-party addon, previous compromise, or anything of sorts. All the victim needs to do is visit a malicious website.
“What we found is different. Our vulnerability lives in the core system itself—no plugins, no marketplace, no user-installed extensions —just the bare OpenClaw gateway, running exactly as documented,” the researchers explained.
Explaining how the bug works, Oasis says OpenClaw runs a local WebSocket server that handles authentication, and more. Nodes, such as companion apps and other machines, connect to the gateway, expose capabilities, run system commands, and access the camera (among other things). The gateway can dispatch commands to any connected node.
Authentication is handled either via a token or a password, and the gateway binds to localhost by default.
Are you a pro? Subscribe to our newsletterContact me with news and offers from other Future brandsReceive email from us on behalf of our trusted partners or sponsorsBy submitting your information you agree to the Terms & Conditions and Privacy Policy and are aged 16 or over.If a victim visits a malicious website, its JavaScript can open a WebSocket connection to localhost, brute-force the gateway password with ease, and authenticate as a fully trusted device.
Once that happens, “the attacker then has full control,” Oasis concluded. “They can interact with the AI agent, dump configuration data, enumerate connected devices, and read logs.”
A fix was deployed 24 hours after initial disclosure, and users are urged to upgrade their instances to version 2026.2.25 or later.
 The best antivirus for all budgetsOur top picks, based on real-world testing and comparisons
The best antivirus for all budgetsOur top picks, based on real-world testing and comparisons➡️ Read our full guide to the best antivirus1. Best overall:Bitdefender Total Security2. Best for families:Norton 360 with LifeLock3. Best for mobile:McAfee Mobile Security
Follow TechRadar on Google News and add us as a preferred source to get our expert news, reviews, and opinion in your feeds. Make sure to click the Follow button!
And of course you can also follow TechRadar on TikTok for news, reviews, unboxings in video form, and get regular updates from us on WhatsApp too.
Sead FadilpašićSocial Links NavigationSead is a seasoned freelance journalist based in Sarajevo, Bosnia and Herzegovina. He writes about IT (cloud, IoT, 5G, VPN) and cybersecurity (ransomware, data breaches, laws and regulations). In his career, spanning more than a decade, he’s written for numerous media outlets, including Al Jazeera Balkans. He’s also held several modules on content writing for Represent Communications.
View MoreYou must confirm your public display name before commenting
Please logout and then login again, you will then be prompted to enter your display name.
Logout Read more Moltbot is now OpenClaw - but watch out, malicious 'skills' are still trying to trick victims into spreading malware
Moltbot is now OpenClaw - but watch out, malicious 'skills' are still trying to trick victims into spreading malware
 Microsoft says OpenClaw is "not appropriate to run on a standard personal or enterprise workstation" — so should you be worried?
Microsoft says OpenClaw is "not appropriate to run on a standard personal or enterprise workstation" — so should you be worried?
 OpenClaw AI agents targeted by infostealer malware for the first time
OpenClaw AI agents targeted by infostealer malware for the first time
 Security experts flag multiple issues in Claude Code, warning, 'As AI integration deepens, security controls must evolve to match the new trust boundaries'
Security experts flag multiple issues in Claude Code, warning, 'As AI integration deepens, security controls must evolve to match the new trust boundaries'
 This 'ZombieAgent' zero click vulnerability allows for silent account takeover - here's what we know
This 'ZombieAgent' zero click vulnerability allows for silent account takeover - here's what we know
 This WebUI vulnerability allows remote code execution - here's how to stay safe
Latest in Security
This WebUI vulnerability allows remote code execution - here's how to stay safe
Latest in Security
 ‘I can think of a couple Pretti Good reasons!’: Hacktivists may have just cracked open ICE and exposed over 6,000 companies working with the DHS
‘I can think of a couple Pretti Good reasons!’: Hacktivists may have just cracked open ICE and exposed over 6,000 companies working with the DHS
 This new phishing campaign uses a fake Google Account security page to steal passcodes and more
This new phishing campaign uses a fake Google Account security page to steal passcodes and more
 Microsoft warns of OAuth phishing campaigns able to bypass email and browser defenses - says 'these campaigns demonstrate that this abuse is operational, not theoretical'
Microsoft warns of OAuth phishing campaigns able to bypass email and browser defenses - says 'these campaigns demonstrate that this abuse is operational, not theoretical'
 Google patches 129 Android security flaws — including a potentially dangerous Qualcomm zero-day
Google patches 129 Android security flaws — including a potentially dangerous Qualcomm zero-day
 'The attack requires no exploit, no user clicks, and no explicit request for
sensitive actions': Experts say Perplexity's AI Comet browser can be hijacked to steal your passwords
'The attack requires no exploit, no user clicks, and no explicit request for
sensitive actions': Experts say Perplexity's AI Comet browser can be hijacked to steal your passwords
 Hackers hijack .arpa domain for phishing scams — hosting malicious websites and domains where no one can spot them
Latest in News
Hackers hijack .arpa domain for phishing scams — hosting malicious websites and domains where no one can spot them
Latest in News
 IKEA's donut-shaped Varmblixt smart lamp is landing early in some stores
IKEA's donut-shaped Varmblixt smart lamp is landing early in some stores
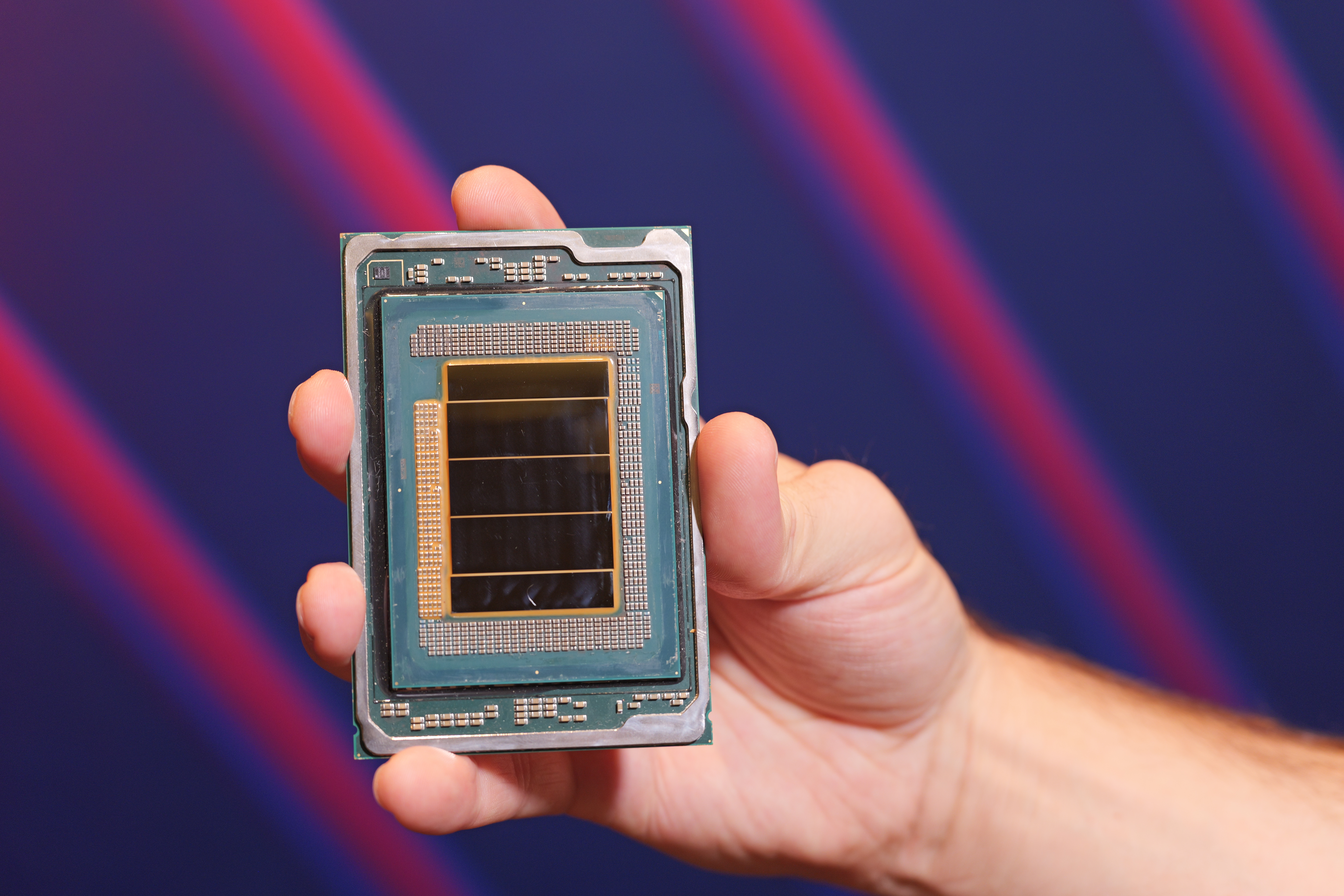 “AI in networks isn’t CPU vs. GPU”: Intel unveils 18A-based Clearwater Forest Xeon 6+ for edge AI and early 6G infrastructure
“AI in networks isn’t CPU vs. GPU”: Intel unveils 18A-based Clearwater Forest Xeon 6+ for edge AI and early 6G infrastructure
 Pokémon Pokopia is the highest-rated Pokémon game since X/Y on Metacritic, and it's not even out on Nintendo Switch 2 yet
Pokémon Pokopia is the highest-rated Pokémon game since X/Y on Metacritic, and it's not even out on Nintendo Switch 2 yet
 Blue Prince just got a Switch 2 release date, alongside 17 more game announcements — here are the top 3 games from the latest Indie World Showcase coming to the Switch consoles that I'm most excited for
Blue Prince just got a Switch 2 release date, alongside 17 more game announcements — here are the top 3 games from the latest Indie World Showcase coming to the Switch consoles that I'm most excited for
 Get up to $50 to watch For All Mankind season 5 with this stellar VPN deal
Get up to $50 to watch For All Mankind season 5 with this stellar VPN deal
 OnePlus 15T’s thin bezels are a boring upgrade, so wait for the OnePlus 16
LATEST ARTICLES
OnePlus 15T’s thin bezels are a boring upgrade, so wait for the OnePlus 16
LATEST ARTICLES- 1'A human-chosen password doesn't stand a chance': OpenClaw has yet another major security flaw — here's what we know about "ClawJacked"
- 2Shark's new robot vacuum has a mopping feature I've never seen before — and it's not the only brand to level-up its mop setup
- 3Seagate reveals Mozaic 4+, its highest-capacity hard drives ever, offering up to 44TB for the next generation of storage
- 4'A marriage of hue and form' — IKEA's donut-shaped Varmblixt smart lamp has started landing in stores early, and we can't wait to get our hands on it again
- 5Forget the Nintendo Switch 2, MWC 2026 is full of brilliant mobile gaming devices, including the Red Magic Astra
